Unified Endpoint Management (UEM): The Complete Guide
Discover how Freshservice integrates with unified endpoint management to simplify IT operations across your entire device ecosystem.
Your IT team manages hundreds of devices running different operating systems, scattered across remote offices and home workspaces. Each device type requires separate tools, creating management silos that drain resources and create security gaps. This is where adopting a single approach that treats Windows laptops, macOS workstations, Android phones, and IoT sensors as parts of one manageable ecosystem. This shift represents more than tool consolidation, creating unified visibility and control that scales with your organization's growth.
Let's examine what unified endpoint management actually accomplishes and why it has become essential for IT teams managing diverse device environments.
What is unified endpoint management?
Unified Endpoint Management (UEM) is a software platform that provides centralized control over all organizational devices through a single management interface. This approach enables IT teams to discover, configure, secure, and maintain smartphones, tablets, laptops, printers, IoT devices, and wearables from one console, regardless of operating system or physical location.
UEM platforms eliminate the operational burden of juggling separate tools for different device types. Instead of managing Windows devices through one system, mobile devices through another, and network equipment through a third platform, you gain unified oversight that treats your entire technology infrastructure as one connected environment.
The platform monitors device performance, enforces security policies, deploys applications, and manages user access consistently across every endpoint. This creates operational efficiency while maintaining the security standards your organization requires.
How UEM evolved from MDM and EMM
Understanding UEM's evolution helps explain why traditional device management approaches no longer meet modern requirements.
Mobile Device Management (MDM) emerged first, giving IT administrators complete control over company-owned mobile devices. MDM solutions focused on device lockdown, location tracking, and converting phones into single-purpose tools. However, this total control approach became problematic as employees began bringing personal devices to work.
Mobile Application Management (MAM) addressed employee privacy concerns by managing only corporate applications and their associated data. Rather than controlling entire devices, MAM solutions allowed administrators to secure business apps while leaving personal data untouched. This approach worked well for mobile apps but left desktop and network devices unmanaged.
Enterprise Mobility Management (EMM) combines MDM and MAM capabilities with additional tools for content management and device provisioning. EMM suites provided comprehensive mobile device oversight but created a significant gap by excluding traditional endpoints like desktops, printers, and network infrastructure.
Unified endpoint management emerged to bridge this gap by combining EMM functions with client management tool capabilities. Modern UEM platforms manage mobile devices alongside desktops, IoT equipment, and specialized hardware through unified policies and workflows. This evolution reflects the reality that today's workplaces include diverse device types that all require consistent security and management approaches.
How unified endpoint management works
UEM platforms operate through a centralized console that connects to agents installed on managed devices. This architecture enables consistent policy enforcement and real-time monitoring across your entire device ecosystem.
The process begins with device discovery and enrollment. When new devices join your network, the UEM platform identifies them and initiates enrollment workflows. Modern zero-touch provisioning reduces this process from hours of IT involvement to 30-45 minutes of automated configuration.
Next, the platform applies configuration policies based on device type, user role, and organizational requirements. These policies define security settings, application permissions, network access rules, and compliance requirements that devices must maintain.
Application deployment follows policy configuration. The UEM console distributes required software, updates existing applications, and removes unauthorized programs according to your approved software catalog. This happens automatically across all managed devices, ensuring consistent application environments.
Ongoing monitoring provides real-time visibility into device health, security status, and performance metrics. The platform continuously evaluates device compliance and triggers automated responses when issues arise, such as isolating compromised devices or applying security patches.
When problems occur, remote troubleshooting tools allow IT teams to diagnose and resolve issues without physical device access. This capability proves essential for supporting remote workers and distributed teams.
Core UEM features and capabilities
Modern UEM platforms deliver comprehensive device management through integrated capabilities that work together seamlessly. The following table outlines core features and their primary functions:
Feature | Primary function | Key benefits |
Device enrollment | Automated device registration and configuration | Reduces setup time from hours to minutes |
Policy management | Centralized security and compliance rule enforcement | Ensures consistent protection across all devices |
Application control | Software deployment, updates, and usage monitoring | Maintains approved software environments |
Patch management | Automated security and system updates | Closes vulnerabilities quickly and consistently |
Remote access | Troubleshooting and support without physical presence | Enables efficient support for distributed teams |
Compliance monitoring | Continuous assessment against regulatory requirements | Simplifies audit preparation and risk management |
Device enrollment and provisioning
Modern device enrollment eliminates manual setup processes through automated workflows that configure devices during first boot. Windows devices use Autopilot integration for Azure AD joining and policy application, while macOS devices leverage Apple Business Manager for Automated Device Enrollment. Mobile devices enroll through zero-touch processes that apply corporate policies without IT intervention.
This automation reduces device provisioning significantly. For example, organizations refreshing 500-device fleets could recover hundreds of IT hours that can focus on strategic initiatives.
Policy enforcement and compliance
UEM platforms enforce security policies consistently across all device types, ensuring encryption requirements, access controls, and compliance standards apply uniformly. Policy engines evaluate device configurations continuously and automatically remediate non-compliant states.
Compliance monitoring supports regulatory requirements like HIPAA, GDPR, and PCI DSS by tracking device access patterns, data handling practices, and security control effectiveness. Automated reporting simplifies audit preparation and demonstrates ongoing compliance efforts.
Patch and update management
Automated patch management addresses the critical challenge of maintaining current security updates across diverse device environments. Modern UEM platforms use AI-driven risk assessment to prioritize patches based on exploit activity, device exposure, and asset criticality rather than just vulnerability scores.
Autonomous patching systems can approve and deploy critical security updates without human intervention. Staged deployment through test, staging, and production rings protects against update failures while maintaining security currency.
Application and data control
Application management ensures users have access to the necessary business tools while preventing unauthorized software installation. UEM platforms maintain approved software catalogs, automate application updates, and remove prohibited programs across all managed devices.
Data protection features include encryption enforcement, data loss prevention, and containerization technologies that separate business and personal information on shared devices. These controls enable secure BYOD programs while protecting organizational data.
Threat detection and response
UEM platforms provide real-time threat monitoring that identifies compromised devices, unauthorized access attempts, and malicious software installations. Integration with Endpoint Detection and Response (EDR) tools creates comprehensive security visibility across your device ecosystem.
Automated response capabilities include device quarantine, user access suspension, and remote data wiping when security incidents occur. These rapid response measures contain threats before they spread to other systems or compromise sensitive information.
The role of ITSM platforms in unified endpoint management
IT Service Management platforms play a crucial role in maximizing UEM effectiveness by connecting device management activities with broader IT service delivery processes. This integration creates comprehensive visibility and streamlined workflows that benefit both IT teams and end users.
Connecting endpoint data with IT service management
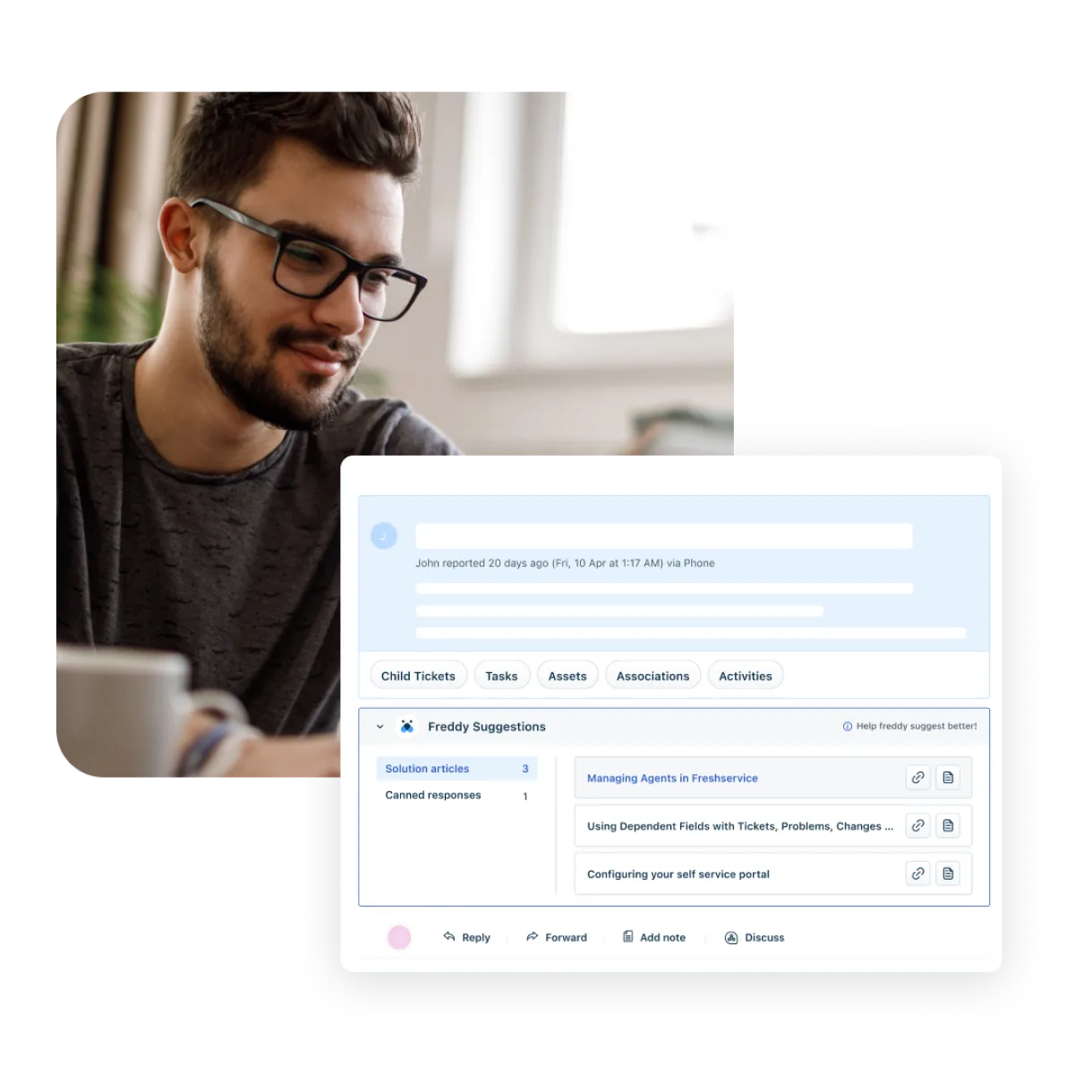
ITSM platforms like Freshservice integrate UEM data to provide complete context for IT service requests and incidents. When users report device issues, service desk agents immediately access device health metrics, recent configuration changes, and compliance status without switching between multiple tools.
This unified view enables faster problem resolution by eliminating information gathering delays. Agents can identify whether reported issues stem from hardware problems, software conflicts, or policy violations, directing them toward appropriate resolution paths immediately.
Managing device lifecycle through service workflows
Device lifecycle management becomes more efficient when UEM capabilities integrate with ITSM workflows. Procurement requests automatically trigger device ordering and configuration processes, while retirement workflows ensure proper data wiping and asset disposal.
Service request fulfillment improves significantly when device provisioning connects to established ITSM processes. New employee onboarding automatically initiates device assignment, configuration, and delivery workflows that are completed before the employee's start date.
Integrating UEM tools with ITSM platforms like Freshservice
Modern ITSM platforms provide native integrations with leading UEM solutions, creating seamless data flow between device management and service delivery systems. These integrations enable automated ticket creation when device compliance issues arise and provide service desk agents with real-time device status information.
Freshservice's asset management capabilities complement UEM platforms by:
Offering end-to-end insights across your IT estate
Identifying outdated assets and risk exposure early to meet requirements and reduce risk
Powering unified service operations with asset intelligence
Key benefits for IT and security teams
UEM platforms deliver measurable improvements in operational efficiency, security posture, and user experience that justify implementation investments.
Security benefits include enhanced remote access control, privilege management that ensures users access only necessary resources, and continuous monitoring for unauthorized devices or software. UEM platforms also provide comprehensive network visibility that helps identify security gaps and compliance violations quickly.
Additionally:
Operational efficiency improves through streamlined patch management that closes security vulnerabilities consistently across all devices.
Application control features ensure users have the necessary business tools while preventing harmful software installations that could compromise system stability.
System recovery capabilities enable IT teams to reset compromised devices remotely, containing malware or ransomware incidents without requiring physical device access. This rapid response capability minimizes business disruption and reduces incident recovery costs.
UEM vs MDM vs EMM vs traditional tools
Understanding the differences between device management approaches helps organizations select appropriate solutions for their environments.
Capability | MDM | EMM | UEM | Traditional tools |
Device types | Mobile only | Mobile + tablets | All endpoints | Platform-specific |
Management scope | Device control | Mobile ecosystem | Complete infrastructure | Individual silos |
Policy consistency | Mobile policies | Mobile policies | Unified policies | Inconsistent |
User experience | Restrictive | Balanced | Flexible | Varies |
IT complexity | Moderate | High | Low | Very high |
Scalability | Limited | Moderate | High | Poor |
Traditional tools create operational silos that require separate expertise, licensing, and maintenance efforts. UEM platforms consolidate these functions while providing superior visibility and control across diverse device types.
UEM vs MDM vs EMM vs traditional tools
Understanding the differences between device management approaches helps organizations select appropriate solutions for their environments.
Capability | MDM | EMM | UEM | Traditional tools |
Device types | Mobile only | Mobile + tablets | All endpoints | Platform-specific |
Management scope | Device control | Mobile ecosystem | Complete infrastructure | Individual silos |
Policy consistency | Mobile policies | Mobile policies | Unified policies | Inconsistent |
User experience | Restrictive | Balanced | Flexible | Varies |
IT complexity | Moderate | High | Low | Very high |
Scalability | Limited | Moderate | High | Poor |
Traditional tools create operational silos that require separate expertise, licensing, and maintenance efforts. UEM platforms consolidate these functions while providing superior visibility and control across diverse device types.
Common use cases and industry examples
UEM platforms address specific business challenges across various industries and organizational scenarios:
Regulatory compliance becomes manageable when UEM platforms enforce encryption requirements across all devices handling sensitive data. For example, healthcare organizations use UEM to ensure HIPAA compliance while enabling mobile access to patient information systems.
Zero-trust security implementations rely on UEM platforms to provide continuous device assessment and conditional access enforcement. Financial services organizations use these capabilities to verify device health before granting access to sensitive applications and data.
Hybrid workforce support enables seamless device management regardless of employee location. This is visible in technology companies that use UEM to maintain security standards while supporting flexible work arrangements that span multiple geographic regions.
BYOD program success depends on UEM capabilities that separate personal and business data while maintaining user privacy. For instance, educational institutions use containerization features to provide secure access to institutional resources on student-owned devices.
Implementation best practices and printable checklist
UEM Implementation Checklist
Define device management policies and security requirements
Assess existing device inventory and management tools
Select a UEM platform that supports all device types
Plan pilot deployment with a representative device sample
Develop user training materials and a communication plan
Configure automated enrollment and provisioning workflows
Establish compliance monitoring and reporting procedures
Test remote troubleshooting and support capabilities
Create incident response procedures for security events
Schedule regular policy reviews and platform updates
Successful UEM implementation begins with a clear policy definition that aligns with organizational security requirements and regulatory obligations. Document device management standards, user access rules, and compliance requirements before platform configuration begins.
Pilot deployments validate platform capabilities and identify configuration issues before full-scale rollout. Select representative devices and users for pilot testing, gathering feedback that informs broader deployment strategies.
User training ensures successful adoption by helping employees understand new security procedures and device management requirements. Develop training materials that address different skill levels and device types, focusing on practical scenarios users will encounter.
Platform maintenance requires ongoing attention to policy updates, security patches, and feature enhancements. Establish regular review cycles that keep UEM configurations current with changing business requirements and security threats.
Challenges and considerations
UEM implementation presents several challenges that organizations must address for successful deployment:
User privacy concerns arise when implementing endpoint monitoring and control capabilities. Address these concerns through clear communication about data collection practices and policy enforcement boundaries. Provide opt-out options for personal devices where legally permissible.
Integration complexity increases when connecting UEM platforms with existing security tools, identity management systems, and business applications. Plan integration testing carefully and allocate sufficient time for troubleshooting connectivity issues.
Cost considerations include licensing fees, implementation services, and ongoing maintenance requirements. Evaluate the total cost of ownership over 3-5 years, including potential savings from operational efficiency improvements and security risk reduction.
Change management challenges emerge when transitioning from existing device management processes to unified approaches. Develop communication strategies that help users understand the benefits while addressing concerns about new procedures and restrictions.
Future trends in unified endpoint management
UEM platforms continue evolving to address emerging technology trends and changing workplace requirements.
Here's how:
Cloud-native architectures have become standard for new UEM deployments, offering improved scalability, faster updates, and reduced infrastructure requirements. Organizations benefit from reduced deployment complexity and more predictable operating costs.
Artificial intelligence integration automates routine management tasks like patch scheduling, compliance monitoring, and threat response. AI-powered systems reduce manual workload while improving response times for security incidents and performance issues.
Zero trust integration moves beyond separate security layers to embed continuous verification directly into UEM platforms. Access decisions now consider real-time device health, user behavior, and environmental factors automatically.
IoT and edge device management capabilities expand UEM scope beyond traditional endpoints to include sensors, controllers, and specialized equipment. This expansion enables comprehensive infrastructure visibility and consistent security policy enforcement.
Check out the service management benchmark report
FAQs
What are typical UEM licensing costs and pricing models?
UEM platforms typically use per-device monthly subscription pricing per endpoint, depending on feature sets and vendor. Cloud-based solutions often include implementation support and regular updates in subscription costs.
Should we choose cloud-based or on-premises UEM?
Cloud-based UEM platforms offer faster deployment, automatic updates, and better scalability for most organizations. On-premises solutions may be necessary for highly regulated environments with specific data residency requirements.
How does UEM integrate with our existing EDR platform?
Modern UEM platforms provide API integrations and data sharing capabilities with leading EDR solutions. This integration creates comprehensive endpoint visibility that combines management data with security telemetry for better threat detection.
What about user privacy concerns with endpoint monitoring?
UEM platforms offer granular controls that separate business and personal data on shared devices. Implement clear policies about monitoring scope and provide users with transparency about data collection and usage practices.
How long does UEM deployment typically take?
Pilot deployments typically complete within 2-4 weeks, while full organizational rollouts require 1-3 months, depending on device count and complexity. Zero-touch provisioning capabilities significantly reduce deployment time for new devices.